Information security
Secure software development and IT services
With BCS, you get a secure ERP and project management system that has been developed in Germany to the highest standards. That's why we place great importance on holistic information security management. Thanks to ISO/IEC 27001 certification, regular security updates, and comprehensive measures for hosting, software development, interfaces, support portal, and BCS app, BCS ensures maximum confidentiality, integrity, and availability of your data—both in the cloud (SaaS) and on-premises. Here you can find out what measures we have implemented to provide you with secure hosting services and a secure product in the form of Projektron BCS.
TÜV-certified quality – secure product Projektron BCS
Projektron GmbH places a high value on information security and has therefore implemented a comprehensive information security management system (ISMS). With the introduction of this system, we have anchored information security in the company's organizational structure and established central processes such as risk management. Our overarching goals in this regard are always the following:
| Confidentiality | Integrity | Availability |
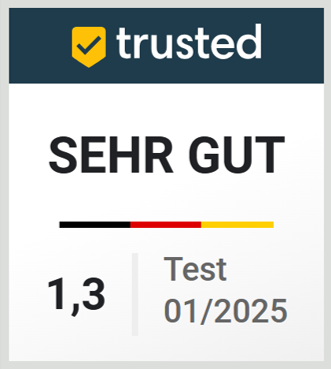
A central element of our information security and quality management is our ISO 27001 certification by TÜV Rheinland. This certification confirms that our processes, systems and controls meet the strict requirements of the ISO 27001 standard. Our ISO/IEC 27001:2022 A1 certification covers not only the operation of development and IT services but also our support and IT administration. Our ISMS is regularly reviewed and adapted to respond to new threats and challenges. This guarantees that our security measures are always up to date and that your data is continuously protected.
Regular security updates and bug fixes
The regular installation of updates is one of the most important security measures that users of Projektron BCS should pay attention to. We are constantly working to identify potential security vulnerabilities and fix them immediately. Updates to our software therefore always include bug fixes and eliminated security risks. Therefore, update your BCS installation regularly to be protected against potential risks in the best possible way.
Product development
Secure software development – secure software: Information security in the development process is essential to offering a software product with Projektron BCS that provides a secure basis for your business requirements and ensures the confidentiality, integrity and availability of your information.
Our measures for secure software development
Access control and authentication | ||||
Role and rights conceptA customizable role and rights concept is a prerequisite for restricting access to data or information to authorized persons. | Single sign-onBCS supports authentication via SAML, Active Directory (LDAP/KERBEROS) or OAuth 2.0 with OpenID Connect. | |||
Guidelines for passwordsProjektron BCS supports guidelines for passwords regarding password complexity and frequency of changes. | 2-factor authenticationThe login can be additionally secured by a second factor generated according to the TOTP procedure. | |||
PasskeysBCS supports Passkeys, a password-free authentication method that replaces passwords with an asymmetric procedure, thereby increasing user-friendliness and eliminating vulnerabilities such as phishing, password theft and weak passwords. | ||||
Data security and protection mechanisms | ||||
Encrypted connectionsEncrypted communication is possible for secure data transfer between Projektron BCS and users or external systems (https, imaps, smtps). | Password vaultPasswords needed for third-party systems can be stored cryptographically secure in a password vault. | |||
Secure passwordsPasswords are secured in Projektron BCS with the PBKDF2 algorithm as well as salt and pepper. | Brute force attacksUser accounts are protected by waiting times or account lockout after multiple failed login attempts. Access to individual accounts can be restricted to certain IP addresses and IP ranges. | |||
Testing and review | ||||
Vulnerability scanningThe software is regularly scanned for known security vulnerabilities. | PentestsPentests are regularly carried out in collaboration with our customers. The results of these tests are continuously incorporated into the development and protection of Projektron BCS. | |||
Automated testingProjektron BCS is tested for both functionality and user-friendliness. Common attack patterns can be checked automatically. Automated tests are integrated into the Continuous Integration (CI) pipeline to ensure that every change to the code is tested immediately. | Integration testsWe perform integration tests to ensure that different components of the software work together securely and that no new security vulnerabilities arise. | |||
Unit testingFor each user story, we develop unit tests to verify correct functionality and security at the code level. | Test coverage reportsWe create test coverage reports that show the coverage of user stories by the tests and ensure that no security-critical areas remain untested. | |||
End-to-end testingWe create end-to-end tests that cover the entire user story and ensure that the application works as expected and is secure. | ||||
Internal security measures | ||||
Definition of security requirementsSecurity objectives and requirements are clearly defined at the beginning of the project. | Security planningWe follow a detailed security plan that describes security measures and procedures. | |||
Team of experts in product developmentA specialized team continuously deals with current IT security issues and implements the latest security measures in Projektron BCS. This ensures that our software always meets the highest security standards. | Internal guideline “Secure Software Development”The internal guideline aims to minimize security deficits and vulnerabilities in the development of Projektron BCS and to respond appropriately to them. This is done by taking into account the SANS 25, which lists the 25 most dangerous and relevant vulnerabilities in software, as well as the OWASP Top 10, which describes the ten most widespread and important vulnerabilities for web applications. | |||
Staff trainingOur developers receive regular training and are made aware of security aspects and best practices. | Awareness programsWe run programs to promote security awareness throughout the development team. | |||
Security documentationAll security requirements, measures and tests are documented in detail. | ReportingWe regularly report on the security status and any incidents that have occurred to relevant stakeholders. | |||
Secure programming and development guidelines | ||||
Coding standards and guidelinesWe adhere to proven coding standards and guidelines to avoid security vulnerabilities. | Code reviews and peer reviewsThe code is regularly reviewed by colleagues to identify potential security issues at an early stage. | |||
Static Code AnalysisTools are used for static code analysis to find vulnerabilities in the source code. | Risk AssessmentPotential security risks are identified and assessed throughout the entire development process. | |||
Vulnerability ManagementA process has been implemented to detect, assess and remediate security vulnerabilities. | ||||
Version Control and Configuration Management | ||||
Version controlWe use version control systems (e.g. Git) to track changes in the code and ensure traceability. | Configuration managementWe ensure that all configurations are securely managed and documented. | |||
Incident response and emergency planning | ||||
Contingency plansContingency plans have been created and are continuously maintained to enable a quick and effective response in the event of a security incident. | Incident responseWe have established a process for responding to security incidents, including analyzing and rectifying the causes. | |||
Hosting / SAAS
We know that a secure system is important to you, especially if you host Projektron BCS with us or our service provider.
Our measures for secure hosting
Location and Availability | ||||
Data Center in GermanyThe data center is located in Germany and complies with high security standards. It is classified as Tier IV with redundant ISP PoPs. | Backup and RecoveryThe hosting includes backups and enables fast recovery when required. | |||
ISO 27001 CertifiedOur data center and security-relevant areas of Projektron are certified according to ISO 27001. The data center also holds additional certifications: VdS ISO 9001 NSL and IS, DIN 14675 for fire alarm systems, and DIN EN 50518. | AvailabilityWe guarantee the agreed availability, which is continuously monitored. | |||
ISO/IEC 27017 & ISO/IEC 27018Our cloud services are certified according to ISO/IEC 27017 (cloud security) and ISO/IEC 27018 (protection of personal data in the cloud). These certifications extend our existing security standards with specific requirements for cloud environments, strengthening data protection, transparency, and clear allocation of responsibilities in cloud operations. | C5 AttestationIn addition, our hosting meets the requirements of the Cloud Computing Compliance Controls Catalogue (C5) of the Federal Office for Information Security (BSI) with a C5 Type 1 attestation. This confirms the appropriateness of the implemented security measures at the time of assessment. A C5 Type 2 attestation, which also verifies the effectiveness of these measures over a defined period, is currently in progress and is expected to be completed in March 2027. | |||
Physical Security and Access Control | ||||
Access ControlThe data center may only be accessed by authorized personnel assigned to specific tasks, and only with prior registration.
| Security PersonnelThe data center is staffed by on-site security personnel 24/7, 365 days a year. | |||
Security Testing and Updates | ||||
Automated UpdatesThe virtual machines and Projektron BCS are updated automatically to ensure you are always on the latest and most secure version. | Maintenance WindowsRegularly scheduled maintenance windows are used to apply updates and patches. In the event of a critical vulnerability, unscheduled updates may be performed with two hours' prior notice. | |||
Penetration TestingOur hosting undergoes annual penetration testing. | ||||
Data and Access Security | ||||
Separate Database ServersCustomer data is stored on separate database servers. This improves performance and allows for the setup of individual interfaces. | SSLAccess to Projektron BCS is provided via an encrypted connection using SSL certificates. | |||
VPN TunnelThe virtual machines are not accessible via the public internet. Projektron accesses them exclusively through VPN tunnels. | FirewallA centralized firewall with strict, customer-specific filtering rules protects against external attacks. A web application firewall can be provided upon request. | |||
Secure Connections via HTTPS/SFTP/SSH & SCPAccess to your virtual machine is exclusively via secure connections (HTTPS/SFTP/SSH), for example to create backups or transfer data (via SCP). | ||||
Additional Services and Training | ||||
KVDOur customers are automatically connected to the configuration versioning service (KVD). This means their configurations are managed within an SVN repository. | TrainingEmployees receive needs-based training on the security of hosting services. | |||
Companies in the IT security industry trust Projektron BCS
Companies in the IT security and software industry also rely on Projektron BCS to manage their projects securely, efficiently, and transparently.
Our web-based solutions meet the highest standards of information security and data protection—a crucial factor for organizations that work with sensitive data.
Support portal & Projektron BCS-App
The following measures provide an overview of the most important security and configuration settings that make the Projektron BCS support portal and Projektron BCS-App even more secure and efficient. Find out how to optimally protect your data and customize the platform to suit your needs.
Our security measures for the support portal and Projektron BCS-App
Support portal | ||||
Transport securityTransport security in the support portal is ensured by the optional but recommended use of HTTPS. | Message exchange and authenticationMessages are exchanged via SOAP, with authentication being ensured by username and password in the SOAP header. The synchronization user should be protected with a strong password because it has extensive rights. This password should be stored in the password | |||
Configuration of the Attributes to be SynchronizedThe attributes to be synchronized can be configured, whereby sensitive attributes can be excluded from synchronization. | Port RestrictionsPort restrictions can be applied to specifically restrict the HTTP exchange between the systems involved. | |||
Projektron BCS-App | ||||
Transport securityThe transport security of the Projektron BCS-App is guaranteed, as it can only be used in conjunction with HTTPS. | Authentication and cookie managementAuthentication is carried out via a username and password, followed by the use of a long-lasting cookie that is stored securely in the memory and removed from the app when you explicitly log out. | |||
Rights application during synchronizationWhen synchronizing from the Projektron BCS-App app to Projektron BCS, the rights set in BCS are applied. | ||||
Interfaces
This is where you will find an overview of the central security aspects when using interfaces in Projektron BCS. Regardless of whether you are integrating Microsoft Exchange, Microsoft 365 (Exchange Online) or Jira, this is where you will learn how to ensure transport security and which authentication and authorization methods are used.
Our interfaces from a security perspective
Microsoft Exchange On-Premises | ||||
Transport securityTransport security for Microsoft Exchange on-premises is ensured by the optional but recommended use of HTTPS. | AuthenticationProjektron BCS supports the BASIC, DIGEST and NTLM authentication types, which are, however, vulnerable to certain attack patterns. BCS does not yet support the modern AD FS authentication type, which is based on OAuth 2.0 and is used by Exchange 2019. | |||
Microsoft Exchange Online | ||||
Transport securityWhen using Microsoft Exchange Online, transport security is guaranteed by the exclusive use of HTTPS. | AuthenticationSecure, token-based authentication provides additional protection when using Exchange Online. | |||
Jira On-Premises | ||||
Transport securityTransport security for Jira On-Premises is guaranteed by the optional but recommended use of HTTPS. | Message exchangeThe message exchange is done via SOAP, where the password of the sync user must be securely protected. | |||
Impersonation and securityAfter logging in via the sync user, impersonation is used to store actions in the context of the logged-in user. | ||||
Jira Cloud | ||||
AuthenticationIn Jira Cloud, authentication is done via an API key on the user via the REST interface in BCS, whereby the API key is securely created and stored. | Security recommendationIt is recommended that Jira Cloud and Projektron BCS be installed on the same system to be able to block ports through a firewall. | |||
User managementOnly the administrator can manage the user assignment mappings in BCS. | ||||

Steffen Späthe
Chief Technology Officer | Navimatix GmbH
At Navimatix, we use BCS for all core processes within our company—from quote generation, project management, and customer and contact management to employee management and our information security management. BCS provides us with a reliable foundation for efficiently handling our day-to-day challenges.

Tanja Maier
Controlling, SSC-Services GmbH
“[The] risk management of [Projektron] helps us, among other things, to meet the requirements of the TISAX and ISO labels. We store agreements such as service level agreements and non-disclosure agreements for the corresponding projects, record whether relevant information values are processed in the project and whether scheduling has been contractually agreed. Risks and, if applicable, opportunities are stored in the project by the project manager.”

Michael Schäfer
Managing Director, Schutzwerk GmbH
"We wanted an all-in-one solution that covers our high security requirements and supports us in handling our audit projects in the area of cyber security. In addition to the use of basic project management functions, especially for many smaller projects, cross-project resource management and automation from service recording to invoicing are essential for us. Projektron BCS also supports us in the efficient implementation of our internal projects, such as certifications."

Carsten Münch
First Business Partner & Team Coordinator Application Management, TÜV Rheinland Service GmbH
"We have implemented single sign-on so that our employees don't have to enter a password and can use a secure and modern login procedure."

Thomas Hackenbuchner
Head of Finance & Administration, MicroNova AG
"When it comes to information security, BCS provides support through the option of assigning additional attributes to projects. For example, we can classify projects in terms of their need for protection or mark whether it is a project with prototype protection. Based on these markings, we can derive and initiate further process steps."

Kevin Botsch
BCS Technical Product Management, Finanz Informatik Solutions Plus GmbH
"As a consulting, development and integration service provider for business applications in the financial sector, software security and transparent processes are important to us. Due to our growth to date and the constantly increasing number of users, user-friendliness and intuitive operation have also become important factors. With Projektron BCS, we have found a system that meets these requirements exactly. In addition, BCS can also be flexibly adapted to our needs and enables us to make numerous process improvements."
Quality and information security management at Projektron GmbH
In addition to secure software development and secure hosting, efficient business processes are at the core of our project management software and our company. That is why we have implemented a comprehensive quality and information security management system.
Quality and information security management at Projektron GmbH