03/19/2026 - Articles
Digital Sovereignty in Business Software: Why “Hosted in Germany” Will Be Crucial in 2026
Cloud software has made companies more efficient, but at the same time has led them into new dependencies: By outsourcing core business systems, companies have not only relinquished control over infrastructure, but increasingly also over legal and operational control. By 2026 at the latest, therefore, the right business software will no longer be determined solely by its feature set or scalability, but by the question of digital sovereignty. Who controls the data, the business logic, and access rights, and under which jurisdiction? This article explains why “Hosted in Germany” is becoming a strategic criterion for resilience, compliance, and business agility in business and ERP software.
What does digital sovereignty mean?
Digital sovereignty refers to the ability of companies to design, control, and further develop digital systems, data, and processes in a self-determined manner. This encompasses not only data protection and hosting location, but also the reduction of unilateral dependencies on providers, clear legal responsibilities, interoperability, the ability to switch providers, and control over decisions related to security and data protection.
For business software, this means specifically: A company must not only know where data is stored, but also who can access systems, under what legal framework the software is operated, and how dependent core business processes are on a single provider.
Key Takeaways: Digital Sovereignty in Business Software
Digital sovereignty encompasses not only data location and jurisdiction, but also interoperability, substitutability, and the reduction of vendor lock-in.
By 2026, digital sovereignty will be a strategic selection criterion for business software. It is not just features that matter, but also jurisdiction, controllability, and resilience.
What matters is not just the server location, but legal control over data, business logic, and access rights.
Services hosted in the US or subject to US jurisdiction can create legal access risks even with EU hosting, for example through the CLOUD Act.
“EU region” or standard contractual clauses often do not solve the underlying problem if providers remain subject to U.S. law or retain administrative access.
A lack of digital sovereignty has concrete consequences: increased compliance efforts, a higher burden of proof, loss of control, contractual risks, and potential reputational damage.
“Hosted in Germany” is a key component of digital sovereignty—with a clear legal framework, reduced third-country complexity, and improved auditability.
Open standards, clear export options, and transparent rights frameworks are central criteria for sovereign business software.
Contents
Digital sovereignty doesn't start with the data center, but with the business logic
When companies discuss cloud strategies today, traditional criteria often still dominate: costs, scalability, features, depth, and integrations. All of these remain important, but they don’t tell the whole story.
Business software is no longer merely a supporting IT tool. It is the company’s operational nervous system. ERP, project management, resource management, CRM, and controlling systems serve as hubs for critical management information that extends far beyond individual processes.
Business software typically bundles:
Customer and contract data
Project calculations, hourly rates, and margins
Resource and capacity planning
Quotation logic, internal roadmaps, strategic priorities
Personal data (HR data, time tracking, roles, skill profiles)
Documents, communication, approvals, and decision-making processes
These systems not only map processes; they represent the business model itself
What “digital sovereignty” really means in a business context
Digital sovereignty does not mean self-sufficiency or avoiding technology. It describes a company’s ability to
legally and organizationally control data, systems, and business processes,
deliberately limit digital dependencies and avoid critical lock-in effects,
manage access, responsibilities, and liability in a transparent manner,
remain capable of acting in the face of regulatory, political, or technical changes,
keep central systems interoperable, auditable, and migratable when necessary.
At its core, it is about freedom of decision-making, controllability, and resilience.
Why Business Software Is No Longer Just a “Tool Issue”
In many companies, project management, ERP, and business coordination systems are still regarded as “organizational tools.” In reality, they have long since become management tools: They determine how projects are prioritized, how resources are allocated, how margins are generated, and how transparently a company operates both internally and externally.
This is precisely why digital sovereignty in business software is now a resilience issue. It is not just about data protection, but about governance, reliability, and strategic control.

The key question is therefore no longer: “Where are the servers located?”
But rather: “Under which jurisdiction does our business logic operate, and what does that mean in the event of an emergency?”
The 5 Pillars of Digital Sovereignty in Business Software
Anyone seeking to assess digital sovereignty should look beyond just the server location. In practice, five key factors are particularly crucial:
1. Legal sovereignty: Under which jurisdiction do data, operations, and support fall? What types of government access are legally permissible?
2. Data sovereignty: Who controls stored data, metadata, keys, roles, and access rights?
3. Operational sovereignty: How dependent is the company in its day-to-day operations on a single provider, its support, APIs, or operating model?
4. Technical sovereignty: How open is the system? Are there interfaces, export options, integration capabilities, and documented migration paths?
5. Strategic sovereignty: Does the software support long-term flexibility, or does it create a lock-in that complicates future changes, audits, or new requirements?
Only the interplay of these five levels reveals how sovereign a business software solution truly is.
Open Source, Open Standards, and Exit Capability
Digital sovereignty does not automatically mean that all business software must be open source. Nevertheless, open standards, documented interfaces, and reliable export options play a central role.
Companies are only sovereign in the long term if they do not confine data, processes, and integrations exclusively within proprietary platform logics. Therefore, questions such as the following are crucial:
Can data be exported in a structured manner?
Are interfaces documented and permanently usable?
Can third-party systems be integrated without complete dependence on the manufacturer?
Is switching providers realistic or only theoretically possible?
Sovereign business software reduces not only legal risks but also technical and economic dependencies.
What “servers in the U.S.” really means for digital sovereignty: The risk isn’t the location, but control
Jurisdiction is a key factor in digital sovereignty, but not the only one. Equally important are control, transparency, interoperability, and the avoidance of structural dependencies on specific providers.
Many organizations feel secure because they say, “Our data is stored in the EU, after all.” Technically, that may be true. Legally, however, it is often not decisive. This is because, with U.S. providers, the geographic location of storage matters less than corporate affiliation—and thus the applicable jurisdiction. This is precisely where the U.S. CLOUD Act comes into play.
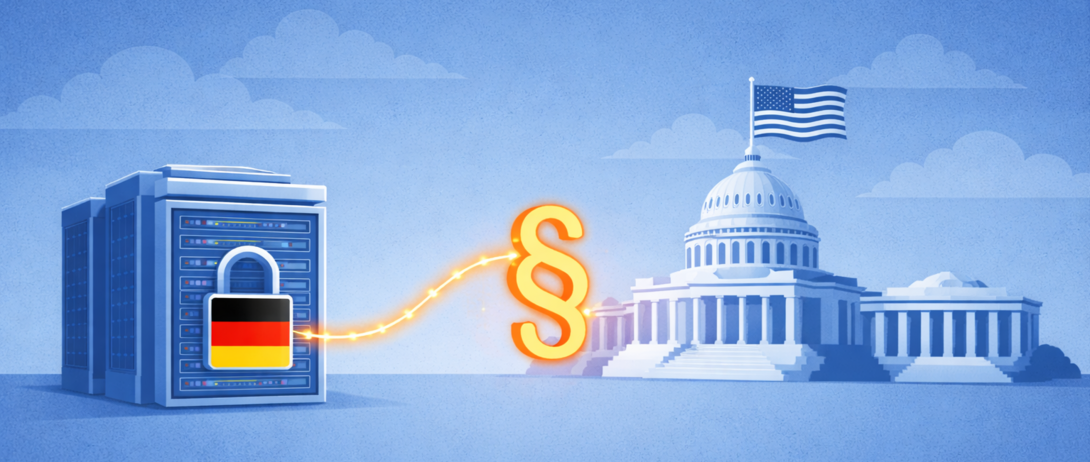
The CLOUD Act: Extraterritorial Access Powers by Law
The Clarifying Lawful Overseas Use of Data Act (CLOUD Act) requires U.S. companies to hand over data to U.S. authorities upon lawful order, regardless of where that data is physically stored.
What matters here is not the location of the data center, but the legal and factual control over the data. A disclosure obligation may exist in particular if the provider is subject to U.S. law,
is responsible for the software, platform, or operational management, or
has administrative access to the systems.
In these cases, a disclosure obligation may apply even if
the servers are physically located in the EU or a European data center is used, or
the customer is a European company.
The CLOUD Act is not an emergency or exceptional law, but permanently applicable U.S. federal law. It applies not only to terrorism or security cases, but also to investigations under general U.S. criminal and security law.
CLOUD Act (USA)
The CLOUD Act (Clarifying Lawful Overseas Use of Data Act) is a U.S. law that was passed by the U.S. Congress in 2018 and signed by Donald Trump. The purpose of the law is to provide U.S. law enforcement agencies with legally secure access to digital data when it is needed for investigations.
At the core of the CLOUD Act is the clarification that U.S. companies can be compelled to hand over stored data to U.S. authorities. This applies regardless of the country in which the servers are physically located. What matters is not the location of the data, but rather the legal control over the company managing the data. As a result, the CLOUD Act has extraterritorial effect.
This is particularly relevant for European companies, as it can lead to a conflict with the GDPR. Personal or business-critical data processed by a U.S. cloud or software provider could theoretically be subject to access by U.S. authorities, even if it is stored exclusively in European data centers. In such cases, European data subjects have only limited transparency and enforcement options under EU standards.
For German and European software providers, this results in a clear distinction: Providers without a U.S. parent company and without legal control by U.S. companies are not subject to the CLOUD Act. This is increasingly perceived as a competitive advantage, particularly in data protection-sensitive industries, in the public sector, and among small and medium-sized enterprises with high compliance requirements.
U.S. software providers, on the other hand, are generally subject to the CLOUD Act, even if they operate data centers in the EU or use European subsidiaries. Technical measures such as encryption or European key management can reduce the risk, but do not alter the fundamental legal possibility of access.
„EU-Region“ schützt nicht vor US-Zugriff
Many U.S. providers advertise “EU Data Residency” or “EU Region Hosting.” While this reduces latency and meets certain data protection requirements, it does not alter the legal ability to access data if:
the parent company is based in the U.S.,
key management, support, or maintenance are handled in the U.S.,
or U.S. personnel have administrative access.
This is precisely what the Stiftung Datenschutz has already explicitly pointed out. A 2025 statement notes, among other things, that providers such as Microsoft cannot rule out access by U.S. authorities, even with European hosting.
The decisive factor here is not whether access occurs regularly, but that:
it is legally possible,
cannot be fully controlled or prevented,
and companies cannot reliably rule it out to customers or supervisory authorities.
Why Standard Contractual Clauses (SCCs) and TIAs Do Not Solve the Problem
Many companies attempt to mitigate the risk through:
Standard Contractual Clauses (SCCs),
additional technical measures,
and Transfer Impact Assessments (TIAs)
However, these instruments have a clear limitation: they are effective only as long as the underlying legal framework remains stable and compatible.
The CLOUD Act, however, is structurally at odds with the GDPR, particularly with:
the principle of purpose limitation,
the transparency requirement,
and protection against disproportionate government access.
A TIA can clearly describe risks, but it cannot eliminate them if a provider is legally obligated to disclose data in cases of doubt. As a result, the TIA often becomes more of a documentation tool than a protective measure.
The “unpleasant triad” for companies with real-world consequences
This constellation creates a structural risk for European companies that cannot be “negotiated away”:

1. Legal uncertainty
In the event of a conflict, it is unclear which law takes precedence: the GDPR or U.S. federal law. This uncertainty does not lie with the provider, but with the data-processing company—that is, the customer.

2. Burden of proof
Companies must demonstrate to customers, regulatory authorities, and auditors why an unauthorized access is unlikely, proportionate, or adequately safeguarded. This is a line of evidence that would be difficult to uphold in court in the event of a breach.

3. Loss of control
Certain access scenarios simply cannot be prevented, either technically or organizationally. In the worst-case scenario, companies may not even be aware that access has occurred, for example, due to confidentiality agreements.
Why the CLOUD Act is relevant today
Although the CLOUD Act is not new, it is regaining relevance due to stricter compliance requirements, audit obligations, and geopolitical dependencies. For companies, this means that it is not only important where data is stored, but also which legal jurisdiction providers, support services, and operating models are subject to in the event of an emergency.
As a result, the CLOUD Act is increasingly becoming a key criterion in the selection of software and cloud providers, particularly for public sector clients, regulated industries, and companies with high standards for data protection and legal control.
The specific consequences of a lack of digital sovereignty regarding U.S.-hosted services
The use of cloud and SaaS services subject to U.S. jurisdiction is not merely a technical decision. It defines the extent to which a company retains control over its own data, processes, and decisions. The consequences are not evident in a single detail, but rather in the overall control and operational model.
1) Compliance becomes the norm; digital sovereignty remains out of reach
As soon as personal data or business-critical information is processed in U.S. SaaS systems, or U.S. providers have de facto control over operations, support, or administration, a permanent state of exception arises.
Digital sovereignty actually means: clear responsibilities, a clear legal framework, and predictable obligations.
US-hosted services have the opposite effect.
The ongoing additional effort includes, among other things:
Transfer Impact Assessments (TIAs) upon implementation and with every relevant change
extensive contracts and supplementary agreements
technical mitigation measures, the effectiveness of which must be regularly re-evaluated
recurring re-assessments in the event of changes in legal situations, court rulings, or geopolitical developments
Added to this is a key point:
Your argument must remain sound even if the rules of the game change.

“Digital sovereignty is not achieved by documenting risks, but by structurally preventing them.”
Those who rely permanently on third-country mechanisms treat compliance as a reactive measure rather than an integrated part of corporate governance.
2) Access scenarios are beyond your control: a core problem of lacking digital sovereignty
A central feature of digital sovereignty is the ability to understand, control, and transparently limit access. This is precisely what is not fully possible with services subject to U.S. jurisdiction.
Even if an instance is operated as an “EU region,” the following remains true:
U.S. law can order access
Disclosure obligations can apply regardless of the storage location
Gag orders can prevent companies from even learning about an access request

As a result, companies lose not only control but also transparency. This is in fundamental contradiction to sovereign IT governance. This is particularly critical for organizations with high requirements for confidentiality and traceability, such as:
the public sector and public contracting authorities
suppliers associated with KRITIS (Critical Infrastructure)
Consulting, legal, and auditing firms
Healthcare and life sciences organizations
Security- or defense-related industries
In these contexts, digital sovereignty is not an abstract idea, but a prerequisite for business and operational viability.
3) Contractual and liability risks: When a lack of digital sovereignty becomes a business risk
Digital sovereignty is increasingly being contractually required, either explicitly or implicitly. Many B2B contracts, framework agreements, and tenders contain requirements regarding:
Data residency and jurisdiction
Subcontractors used
Auditability and control rights
Record-keeping for access from third countries
They fail as early as the eligibility or prequalification phase. They must negotiate costly and time-consuming special agreements. They face additional liability risks, such as those arising from contractual penalties or special termination rights.
They fail as early as the eligibility or prequalification phase.
They must negotiate costly and time-consuming special agreements.
They face additional liability risks, such as those arising from contractual penalties or special termination rights.
A lack of digital sovereignty thus becomes not only a compliance issue, but a direct competitive disadvantage, particularly compared to providers who operate their business software under clear European or German jurisdiction.
4) Reputational damage does not arise only from data breaches
A common misconception: Reputational damage arises only from security incidents or leaks.
In practice, however, even a public discussion about:
transfers to third countries
potential government access
unclear or contradictory documentation
can be enough. Especially in small and medium-sized enterprises (SMEs), where trust, long-term relationships, and personal connections are crucial, the impression of a lack of digital sovereignty can cause significant damage, even without a formal data breach.
Digital sovereignty is thus also a reputation and trust factor.
Digital Sovereignty in Practice: When Business Software Becomes an Operating Model
Digital sovereignty is not determined by individual features or user interfaces, but rather where business processes converge. In many European companies, this reality has already been achieved: core operations, communication, and decision-making rely on a few highly integrated cloud platforms.
This is not about “good” or “bad” providers. It is about risk profiles resulting from jurisdiction, operating models, and control capabilities.
In Europe, the following U.S.-based services in particular are widely used for business-critical purposes:
As long as these systems are used in isolation, the risk often remains abstract. But as soon as project management, communication, documents, approvals, and operational decisions converge on them, the dependency is no longer just “IT.” It is the business model.
The Strategic Core of Digital Sovereignty
You’re not just outsourcing hosting.
You’re outsourcing legal control, accountability, and—when in doubt—decision-making authority.
Digital sovereignty means consciously keeping this control within your own sphere of influence. Business software hosted in the U.S. makes this structurally difficult, regardless of how powerful or widely used the tools are.
Popular with service providers, critical for digital sovereignty: ERP and project management systems under U.S. jurisdiction
Service providers in particular—whether they are consulting firms, agencies, IT service providers, engineering firms, or project management companies—often rely on established project management and ERP-related cloud systems from the U.S. This is understandable: rapid implementation, deep integration, and extensive ecosystems. At the same time, these systems centralize particularly sensitive data in one location, making the jurisdiction issue business-critical.
Solutions widely used in Europe that have headquarters in the US and hosting or access subject to US jurisdiction include, among others:
Atlassian (Jira, Confluence Cloud): project management, backlogs, documentation, internal decision-making processes
Salesforce (including PSA and ERP extensions): customer contracts, project finances, forecasts
Oracle (NetSuite): Financial data, project billing, resource planning
Workday: HR, role, and capacity data
ServiceNow: Service and project processes, internal workflows
Microsoft (Dynamics 365, Project, Planner): Project, customer, and company data closely integrated with M365
In practice, this is where the core processes of the service business converge: hourly rates, quotation logic, project margins, customer priorities, capacity utilization, escalations, internal evaluations. This makes these systems not just operational tools, but digital representations of the business model.
The risk arises less from individual functions and more from the concentration of business-critical information under a legal jurisdiction that does not guarantee European companies sufficient control in the event of an emergency. Even with “EU region” promises, the dependence on U.S. law remains, including potential access or disclosure obligations.
For service providers, this means, specifically
Organizations that use project management or ERP systems hosted in the U.S. are not only transferring data but also operational control to a legally uncertain environment. And this is precisely what is increasingly coming into conflict with customer requirements, tenders, compliance regulations, and the organization’s own standards for resilience.
Why Digital Sovereignty Is Becoming a Competitive Advantage in Business Software
Many companies still view project and ERP software as mere organizational tools. In practice, however, they are key management tools. They determine how quickly decisions are made, how reliably planning is carried out, and how clearly business relationships are visible.

Business software manages:
Delivery capability and prioritization
Resource allocation and utilization
Margins, forecasts, and financial transparency
Internal coordination, approvals, and escalations
As a result, it is not merely supportive but crucial to competitiveness.
However, if this control tool operates in a legally uncertain environment, the efficiency gains are reversed: Speed turns into fragility. Scaling turns into dependence.
Digital sovereignty in business software structurally counteracts this effect.

What “Hosted in Germany” Means in Terms of Digital Sovereignty
Business software “Hosted in Germany” does not stand for isolationism or ideology, but for predictable operating conditions. At its core, this means:
Data storage and operations under German law: Clear legal foundations instead of competing jurisdictions.
Clear responsibilities regarding audits and contracts: Liability, access, and traceability can be clearly assigned.
Significantly reduced complexity related to third countries: No ongoing transfer assessments, no geopolitical dependencies.
Stronger ability to justify decisions externally: To customers, data protection officers, auditors, certification bodies, and contracting authorities.
The result is not “more security at any cost,” but less friction, less uncertainty, and less additional effort in day-to-day operations. Digital sovereignty thus becomes an economic advantage.
From “Can” to “Must”: A Reality Check on Sovereignty for Decision-Makers
Digital sovereignty is no longer an abstract topic for the future. For many organizations, it is already business-critical today. A quick reality check will reveal whether it is still a “nice-to-have” or already a “must-have.”
Self-assessment: How business-critical is digital sovereignty for your organization?
Select one level per statement. Higher levels increase the score more strongly.
- How severely would an outage or forced provider change impact your core business within a few days?
- How sensitive is the information in your business software (e.g. pricing conditions, margins, proposal logic, roadmaps)?
- To what extent do you process personal data in daily operations (e.g. timesheets, roles, skills, performance records)?
- To what extent are you affected by regulation (e.g. critical infrastructure, regulated industries, public sector)?
- How binding are commitments regarding data residency or jurisdiction in your contracts?
- What is the level of audit and certification pressure (e.g. ISO 27001, TISAX, industry-specific standards)?
U.S. Tech Giants vs. European ERP and Business Software: A Structural Comparison from the Perspective of Digital Sovereignty
The decision between a U.S.-dominated cloud stack and European ERP and business software operated under German jurisdiction is not a matter of preference or ease of use. It is a strategic choice regarding governance, control, and business resilience.
The differences rarely lie in the interface or feature set, but almost always in the risk and control model. That is precisely where the decision is made as to whether digital sovereignty is gained or lost.
Jurisdiction & Access: Sovereignty vs. Structural Uncertainty
| US stack (e.g. Atlassian, Salesforce, Microsoft, Oracle) | European ERP and business software “Hosted in Germany” |
|---|---|
|
Providers are subject to US federal law (including the CLOUD Act)
|
German or European law as the sole legal framework
|
|
Government access legally possible – even when hosted in EU data centers
|
Clear allocation of responsibilities between provider and customer
|
|
Organizations cannot fully prevent or comprehensively audit access
|
Access governed exclusively by German law and documented procedures
|
|
Transparency and disclosure obligations towards customers are limited
|
High level of traceability and legal certainty
|
structurally uncertain access conditions
predictable jurisdiction and controllability
Compliance Effort & Auditability: Continuous Safeguarding vs. Built-in Sovereignty
| US stack (e.g. Atlassian, Salesforce, Microsoft, Oracle) | European ERP and business software “Hosted in Germany” |
|---|---|
|
Regular Transfer Impact Assessments (TIAs) required
|
No third-country data transfer, no extraterritorial jurisdiction
|
|
Dependence on political and legal frameworks (e.g. DPF, SCCs)
|
Significantly reduced complexity for GDPR, ISO 27001, and audits
|
|
High coordination effort with data protection, legal teams, and external advisors
|
Clear positioning towards customers, auditors, and regulatory authorities
|
|
Compliance becomes an ongoing project rather than a stable state
|
Compliance is embedded in the architecture, not an afterthought
|
continuous compliance effort with high resource consumption
integrated, scalable compliance
Business Criticality for Service Providers: Platform Dependency vs. Controllable System Architecture
| US stack (e.g. Atlassian, Salesforce, Microsoft, Oracle) | European ERP and business software “Hosted in Germany” |
|---|---|
|
Project, customer, HR, and financial data are distributed across multiple systems
|
Centralized control of projects, resources, finances, and organizational processes
|
|
Deep dependency on proprietary platform ecosystems
|
Clear operating models and transparent exit strategies
|
|
High switching costs – exit scenarios often only theoretical
|
Reduced lock-in through European contract and licensing models
|
|
Business model control heavily depends on the vendor ecosystem
|
Business logic remains under the company’s control
|
platform dependency with loss of control
controllable, sovereign system architecture
Tenders & Customer Requirements: Justification Pressure vs. Built-in Trust
| US stack (e.g. Atlassian, Salesforce, Microsoft, Oracle) | European ERP and business software “Hosted in Germany” |
|---|---|
|
Increasing exclusion or scrutiny mechanisms in public procurement processes
|
Positive signal in tendering and selection procedures
|
|
Additional audits for critical infrastructure-related or regulated customers
|
Stronger positioning with security- and compliance-sensitive clients
|
|
Increased need for explanations and documentation in contracts
|
Fewer special clauses, fewer exceptions, fewer negotiation loops
|
|
Additional liability and reputational risks
|
Trust through clear legal frameworks instead of constant justification
|
constant need for justification
structural trust advantage
Interoperability, Exit and Vendor Dependency: Platform Lock-in vs. Controllable Switching Options
| US stack (e.g. Atlassian, Salesforce, Microsoft, Oracle) | European ERP and business software “Hosted in Germany” |
|---|---|
|
Proprietary platform ecosystems with strong dependency on vendor logic
|
Clearer integration and operating models
|
|
Data export and migration often complex or only partially standardized
|
Better predictability for export, migration, and system changes
|
|
Switching costs increase with every additional integration
|
Lower structural dependency on global platform providers
|
|
Technical development and roadmap are largely controlled by the vendor
|
Greater control over long-term system architecture and operating model
|
technical and economic lock-in risks
greater flexibility and architectural control
Business coordination software under German jurisdiction
Modern business software serves as a concrete example of how digital sovereignty requirements can be implemented, as it takes into account not only the hosting location but also the entire operational, security, and governance model. Key factors here include jurisdiction, transparency regarding access and roles, the degree of integration of business-critical processes, the auditability of operations, and dependence on proprietary platform structures.
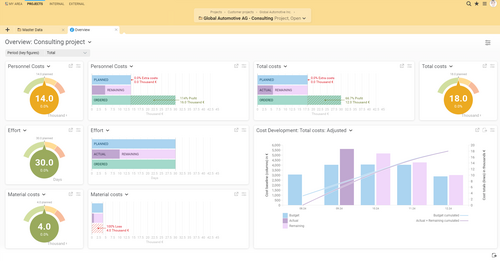
BCS exemplifies this approach. Unlike traditional project management tools or isolated ERP modules, BCS, as business coordination software, follows a consistently integrated model: Core business processes are not connected via interfaces but are mapped within a single system. Project management, resource planning, time tracking, billing, as well as controlling and forecasting are directly interlinked, forming a consistent operational and financial management framework.
BCS brings together, among other things:
Project and portfolio management
Resource and capacity planning
Time tracking, billing, and performance reports
Controlling, forecasts, and management reports
This creates a unified data foundation that not only ensures transparency but also enables reliable decision-making across the entire value chain. BCS thus does not merely map individual functions but rather the core business logic of service-oriented companies.
Predictable Jurisdiction and Integrated Sovereignty
A key difference from many international cloud solutions lies in the underlying operating model. BCS is operated under German jurisdiction, with hosting in German data centers and clearly defined responsibilities between the provider and the customer. This eliminates dependence on U.S. law and extraterritorial access laws.
For companies, this means: business-critical information remains in a legally controllable and auditable environment—from project data and margins to internal management and decision-making processes.
Information Security and Transparent Operations
BCS can be deployed both on-premises and as a SaaS solution. In the cloud version, access is encrypted, and operations are based on documented security and governance processes.
These include, among other things:
ISO/IEC 27001-certified information security management
Operation in a highly classified data center in Germany
A fine-grained, role- and organization-based permissions model
Against this backdrop, certifications such as “Software Made in Germany” and “Software Hosted in Germany” are more than just seals of approval. They represent an operational model in which the hosting location, security measures, and responsibilities are clearly defined and transparently established.



The key difference, therefore, lies not in the range of functions but in the structure: Digital sovereignty here does not result from additional safeguards but is an integral part of the system design.
Best Practices: Digital Sovereignty in Action with BCS
The use of BCS in various organizations demonstrates how digital sovereignty in business software actually impacts day-to-day operations. These real-world examples make it clear that the issue is not merely about hosting or legal jurisdictions, but rather about how securely, transparently, and controllably core business processes can actually be operated.
Westernacher Solutions GmbH
Westernacher Solutions GmbH develops IT solutions for particularly sensitive sectors, including public administration, the judiciary, the church, and notary offices. In these contexts, data protection, traceability, and audit-proof processes are not merely additional requirements, but fundamental prerequisites for day-to-day operations. Projects often navigate the tension between regulatory requirements, individual client needs, and long-term operational models.
As project complexity grew and demands for documentation and transparency increased, it became clear that isolated tools and fragmented processes were no longer sufficient. Westernacher needed a solution that not only supports individual tasks but enables end-to-end control across projects, resources, and the organization.
Against this backdrop, the decision to adopt Projektron BCS was a deliberate one: the goal was to establish a central platform that addresses both operational workflows and governance requirements. Today, BCS serves as an integrated system that brings together project planning, resource management, controlling, and administrative processes, thereby creating a consistent data foundation for all stakeholders.
A key benefit lies in standardization: processes are not only documented but also managed in a structured manner. Roles, responsibilities, and decision-making paths are clearly defined and traceable at all times. This creates transparency that supports both internal management and external requirements, such as those arising from audits or customer projects.

Benjamin Schlötke, Project Office Lead, Westernacher Solutions GmbH
Westernacher Solutions has been working with BCS since January 2010, and right from the start we saw significant improvements in our workflows. Tasks, roles, and responsibilities are clearly structured with the help of BCS. This allows us to create transparency for company management, department and project managers, and employees.
gematik: Transparent Resource Planning in a Complex Matrix Organization
gematik GmbH is responsible for key components of Germany’s digital health infrastructure—an environment characterized by stringent regulatory requirements, complex coordination processes, and a multitude of concurrent projects. As a matrix organization, gematik operates with diverse teams, roles, and responsibilities that must be coordinated across projects.
Prior to the implementation of BCS, project and resource planning relied on several in-house developed solutions. However, these could no longer keep pace with the increasing complexity and the growing need for company-wide transparency and controllability. In particular, the lack of integration led to data silos and made reliable planning difficult.
The goal of the implementation was therefore clear: a central platform that consistently maps resources, projects, and capacities and makes them analyzable. At the same time, the solution had to meet the high requirements for data protection and access control, as sensitive information is processed across the organization.

Mirko Richter, People Analyst, gematik GmbH
Transparent, cross-departmental resource planning with BCS is a major advantage. Combined with the many customizable reporting views, we now get exactly the information we need. It was particularly important to us to have an appropriate permissions and roles framework that protects sensitive information.
msg global solutions: Unified project management across international locations
msg global solutions is an internationally active IT and consulting firm with numerous subsidiaries and project teams located around the world. As the company grew, the need for consistent project management increased significantly: disparate systems, local solutions, and customized processes made comparisons difficult and led to inefficiencies.
Especially in an international context, it becomes clear that project management is more than just operational planning. It is about uniform standards, transparent data, and the ability to manage projects in a comparable manner across national borders. At the same time, local requirements—such as those related to regulation or billing—must continue to be taken into account.
The implementation of BCS therefore aimed to create a central platform that integrated all project-related processes—from planning and time tracking to billing. A key factor was the creation of a unified database that enables both operational control and management reporting.
Today, BCS is used across the entire group and forms the foundation for consistent project organization across more than 20 countries. The software makes it possible to establish global standards while simultaneously responding flexibly to local specifics. This not only creates efficiency but also sustainably improves the manageability of a complex international business model.
An additional advantage lies in the ability to systematically map different regulatory requirements. This is an aspect that is becoming increasingly important, particularly in the context of digital sovereignty and compliance.

Peter Schürmann, Head of Global Project Management, msg global solutions Deutschland GmbH
We use BCS centrally for over 23 of our own country organizations. We needed a central data source and a consistent system for all time tracking, postings, and allocations. All planning, resource allocation, time tracking, and billing are handled within a single BCS instance.
What these examples have in common
These three use cases illustrate that digital sovereignty is not an abstract compliance issue, but rather has a direct impact on manageability, transparency, and resilience. When projects, resources, services, and key performance indicators converge in an integrated system, the business software itself becomes part of the operating model.
In these practical examples, BCS demonstrates that digital sovereignty arises not only from formal assurances, but from a combination of integrated system logic, clear responsibilities, transparent access models, and a legally predictable operational framework. This is precisely what distinguishes mere cloud usage from sovereign digital control.
Fazit: Digitale Souveränität schlägt Bequemlichkeit
By 2026, digital sovereignty will no longer be purely an IT or compliance issue. It concerns the question of how independently, controllably, and resiliently companies can operate their business-critical systems. This includes jurisdiction and data protection as well as interoperability, the ability to exit, transparent access models, and the reduction of unilateral vendor dependencies.
Those who outsource core business, ERP, and project-related processes to third-party systems are not only deciding on functionality but also on controllability, traceability, and long-term freedom of action. This is precisely why digital sovereignty is becoming a strategic selection criterion for business software.
“Hosted in Germany” is an important building block in this context, but true digital sovereignty only emerges when combined with clear responsibilities, auditable processes, transparent rights models, and a controllable system architecture.
FAQ on Digital Sovereignty
What does digital sovereignty mean in a business context?
What does digital sovereignty mean in a business context?
Digital sovereignty means being able to control data, systems, and digital processes legally, organizationally, and technically.
What is the difference between digital sovereignty and data sovereignty?
What is the difference between digital sovereignty and data sovereignty?
Data sovereignty primarily concerns control over data. Digital sovereignty goes further and includes systems, operating models, dependencies, interfaces, and legal frameworks.
Why is digital sovereignty becoming increasingly important for business software?
Why is digital sovereignty becoming increasingly important for business software?
Because business software now represents core business logic, resource management, financial data, and internal decision-making.
Is it sufficient if data is stored in the EU?
Is it sufficient if data is stored in the EU?
No. In addition to data location, jurisdiction, access rights, support structures, and administrative control are crucial.
What role do open standards and interfaces play?
What role do open standards and interfaces play?
They reduce vendor dependency and improve interoperability, data portability, and migration options.
Is open source essential for digital sovereignty?
Is open source essential for digital sovereignty?
Not necessarily. What matters more is whether a system is transparent, controllable, integrable, and usable long-term without critical lock-in.
What risks arise from a lack of digital sovereignty?
What risks arise from a lack of digital sovereignty?
Typical consequences include increased compliance effort, audit challenges, loss of control, contractual risks, and limited switching options.
Why can “Hosted in Germany” be an advantage?
Why can “Hosted in Germany” be an advantage?
Because hosting under German jurisdiction can provide clear legal responsibilities, better auditability, and reduced third-country complexity.

About the Author
Francisco Josué Gutendorf is the Managing Director of Projektron GmbH and is responsible for the company’s strategic direction in the areas of business software and project management. With many years of experience in developing and positioning software solutions for organizations of all sizes, he combines an entrepreneurial perspective with a deep understanding of technological dependencies and control mechanisms. At the heart of his work is the question of how companies can secure their digital sovereignty through the targeted use of software. In this context, he addresses topics such as data sovereignty, vendor independence, governance structures, and the sustainable design of digital infrastructures. Under his leadership, BCS has been consistently developed as a solution that creates transparency, strengthens control, and empowers organizations to manage their processes independently and with long-term stability. His perspective is shaped by the conviction that digital tools not only increase efficiency but also play a decisive role in determining how independent, capable, and resilient companies remain in an increasingly interconnected world.
More interesting articles on the Projektron blog

Comparison: ERP for service providers
For service providers, the choice of ERP system determines efficiency, transparency, and revenue. Our comparison presents the 10 best solutions, explains which features really matter, and provides valuable guidance for your selection. Find the ERP system that truly drives your business forward!

Project Management Software Comparison
Get an up-to-date overview: We compare 15 of the most popular and best project management software solutions. Start here, explore the market, and make your own comparisons!
Project Organization
Project success starts with the right organizational structure. Learn about common project organization models and find the one that best fits your project landscape and business strategy.
Selecting a PM Software
If your SME or enterprise is selecting project management software, you may not know where to start. This guide leads you to the right decision in 9 steps.